- Lazarus Group, the infamous hacking gang from North Korea, purportedly attacked KelpDAO and compromised cross-chain message verification nodes and fed them falsified blockchain data.
- The attackers used a DDoS attack to force the system to rely on compromised RPC nodes, allowing a fake cross-chain message to move rsETH tokens without authorization.
- KelpDAO paused rsETH contracts across Ethereum and layer-2 networks while investigating with LayerZero and other partners, stating the incident did not affect other assets.
KelpDAO, a decentralized finance project, has suffered a breach, with a total stolen amount estimated to nearly $300 Million. The attack is reportedly believed to be from an unknown group of state sponsored hackers operating from North Korea.
The group attacked on April 18 and exploited a vulnerability to execute malicious logic via the project’s cross-chain messaging system. Blockchain security experts suspect that the Lazarus Group is responsible for this attack because they frequently conduct large thefts from DeFi projects.
The total stolen assets is about 116,500 rsETH tokens which is the equivalent of approximately $293 Million at current market rates. The hackers moved the stolen assets quickly to Tornado Cash, a service that mixes cryptocurrencies to obfuscate transaction trails.
KelpDAO made the announcement regarding the incident on the same day after detecting that there were some suspicious cross-chain transactions involving their rsETH token. Also, the protocol’s team responded to this discovery by pausing all rsETH contracts on the Ethereum mainnet and on several layer 2 networks.
Also, they have launched an investigation in conjunction with their partners (LayerZero, Unichain, etc.) to determine how the attack happened and more importantly, how they can prevent another incident from occurring in the future.
Attackers Exploited Cross-Chain Message Verification System
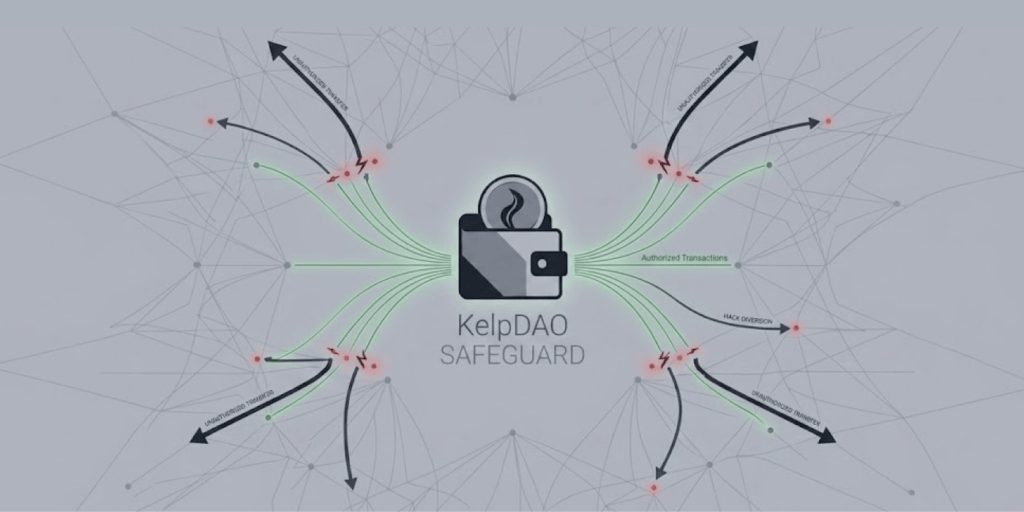
The hackers did not break into KelpDAO’s main contracts directly. Instead, they targeted the verification layer that validates cross-chain messages for the rsETH token. This system is known as a Decentralized Verifier Network or DVN, it acts as a checkpoint for messages moving between different blockchains.
According to details shared by LayerZero on April 20, the attackers compromised specific RPC nodes that the verifier relied upon. They fed these nodes falsified blockchain data. At the same time, they launched a DDoS attack against healthy RPC nodes. This forced the system to depend on the compromised ones for information.
The fake data made the verification layer accept a fraudulent cross-chain message as legitimate. The system confirmed transactions that never actually occurred on the main blockchain. This loophole allowed the hackers to move rsETH tokens out of the platform without any proper authorization.
The United States government has previously linked the Lazarus Group to numerous crypto heists. A few years ago, the US Treasury Department sanctioned the group for stealing over $600 million in cryptocurrency from Axie Infinity’s Ronin Network; that attack remains one of the largest crypto thefts in history.
Lazarus Group Likely Responsible Based on Attack Patterns
LayerZero stated that preliminary indicators from the attack point toward a highly sophisticated state actor – the company specifically named North Korea’s Lazarus Group as the likely culprit. They further narrowed it down to a sub-group known as TraderTraitor.
This would not mark the first major crypto theft tied to Lazarus in recent months. The group also stands accused of stealing $280 million from the Drift Protocol. A post-mortem report on that attack revealed a carefully planned six-month operation. The hackers reportedly sent agents to industry conferences and deposited $1 million into the project to gain access.
The Federal Bureau of Investigation has consistently warned about North Korean cyber operations targeting the cryptocurrency sector. The FBI stated in an advisory that the DPRK uses sophisticated social engineering tactics to infiltrate decentralized finance platforms, these tactics often involve posing as legitimate investors or recruiters.
KelpDAO confirmed that the incident only affected the rsETH token contracts. The protocol stated that no broader contagion has spread across other applications or assets within its ecosystem, however, the stolen amount represents one of the largest crypto heists so far in this year.
Investigation Continues with Help from Industry Partners
The KelpDAO team continues working with multiple partners to investigate the breach. LayerZero, which provides the cross-chain messaging infrastructure, has joined the probe. Unichain and other unnamed partners are also assisting.
The project has not yet announced any plans for reimbursing affected users. Typically, DeFi platforms that suffer major hacks either negotiate with the attackers for a return of funds or launch a treasury-based compensation program. In some cases, they simply write off the loss.
Blockchain analytics firms will likely track the stolen funds as they move through Tornado Cash and other mixers. However, once money enters such privacy tools, tracing it becomes extremely difficult. Law enforcement officers have only very rarely recovered illegally obtained assets from North Korean cybercriminals.
Data breaches present a different challenge, when BitMart user emails were exposed, cybersecurity experts warned that affected users face increased risk of phishing attacks, demonstrating that crypto security must address both asset protection and data privacy.
The attack indicates that there are still serious weaknesses in the security of the cross-chain messaging systems. As DeFi projects become more interconnected – the attack surface for sophisticated hackers continues to grow.
